Contained within the pages of the Committee Report 22 of 108 – House Report 113-102 – NATIONAL DEFENSE AUTHORIZATION ACT FOR FISCAL YEAR 2014 are references to certain vulnerabilities of tactical data links.
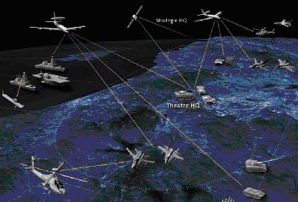
Tactical Data Links (TDLs) involve transmissions of bit-oriented digital information which are exchanged via message formats used in support of joint and combined operations. They can provides real-time, jam-resistant secure transfer of combat data, voice and relative navigation information between widely dispersed battle elements.
“The committee believes that future conflicts against threats with anti-access/area-denial capabilities could see significant threats to U.S. airborne and ground tactical data links. However, the committee is concerned that many such data links are not currently designed or funded to operate against a robust electromagnetic warfare threat. Therefore, the committee directs the Secretary of Defense, to provide a classified briefing to the congressional defense committees by October 1, 2013, that describes the potential vulnerabilities of current and planned tactical data links, along with a summary of development efforts to address these vulnerabilities” (source: Congressional Record: House Committee report http://thomas.loc.gov/).
It should be noted that China has developed, as early as 2007 what is called a virtual road map for attacking tactical data link communications:
“To assist the PLA (People’s Liberation Army) in its goal of attacking deployed aircraft carrier battle groups, two PLA Air Force (PLAAF) authors, Sun Yiming and Yang Liping, have built a virtual roadmap for attacking joint U.S. data control systems and military communications. They have carefully consulted dozens of corporate web sites and military tactical data link operator guides, as well as North Atlantic Treaty Organization (NATO) and U.S. military tactical and technical manuals, to produce a virtual guidebook for electronic warfare and jamming to disrupt critical U.S. cooperative target engagement and command, control, communications, computers, and intelligence, surveillance and reconnaissance (C4ISR) data links: Tactical Data Links in Information Warfare” (source: China’s Nuclear Forces: Operations, Training, Doctrine, Command and control Campaign Planning http://www.strategicstudiesinstitute.army.mil/pubs/summary.cfm?q=776).
In addition there is a Chinese publication for sale on Amazon currently by unknown author/authors detailing research regarding information warfare tactical data link communications in war (paperback) Source: http://www.amazon.com/information-warfare-tactical-data-paperback/dp/756351063X.
“One of the counters to some of the adversary electronic warfare capability is that network integration,” said recently Lt. Gen. Herbert Carlisle, the U.S. Air Force’s deputy chief for operations, plans and requirements. “Even active electronically scanned array radars can be attacked, but it takes a dedicated effort to jam those systems. A combination of sensor fusion and networking could overcome such attacks however” (source: C4I Technology News: Defeating enemy Electronic Warfare through Tactical Data Links and Network Integration http://c4i-technology-news.blogspot.com/2012/02/defeating-enemy-electronic-warfare.html).
See article: PLA war hackers plan on switching off the U.S. Navy http://www.theregister.co.uk/2007/09/10/chinese_military_net_attack_circus_rolls_on/
See video: TCG’s Ground Tactical Data Links http://www.youtube.com/watch?v=j4Mov4fZLhg
See also: The Evolution of Strategic Communication and Information Operations – Subcommittee on Emerging Threats and Capabilities http://www.youtube.com/watch?v=xaC-dccgal8